Data Security with Microsoft Purview
The right tool to ensure data protection and governance
Cybersecurity is a constantly shifting landscape. As our digital world continues to grow, so do the risks. According to research, 83% of organizations experienced more than one data breach in their lifetime, of which 20% of data breaches are due to internal actors with an average cost of $15.4M when a malicious insider is involved. The potential cost is significant and cannot be ignored. Data leaks and theft might be overshadowed by external threats in the past. However, they have become one of the most common vulnerability and risks that organizations need to address.
Recent Microsoft research also shows that 80% of the decision makers purchased multiple products to meet compliance and data protection needs, with a majority of them purchasing more than three products. Managing a fragmented solution landscape brings more complexity to the security teams with additional costs and efforts to bring siloed signals together while building a unified remediation plan.
Why is data security so difficult?
Organizations need to secure data in multiple channels, including emails, messages, shared storage, cloud apps, and devices, on top of managing a fragmented solution landscape

Data is the oxygen of an organization’s digital transformation. As organizations and individuals rely more and more on data, the creation and consumption of data are constantly growing. It’s hard to imagine that people around the globe create 2.5 quintillion bytes of data and send 333.2 billion emails every day. Every organization is experiencing the explosion of data growth and needs to rethink their approach in managing and protecting their data.
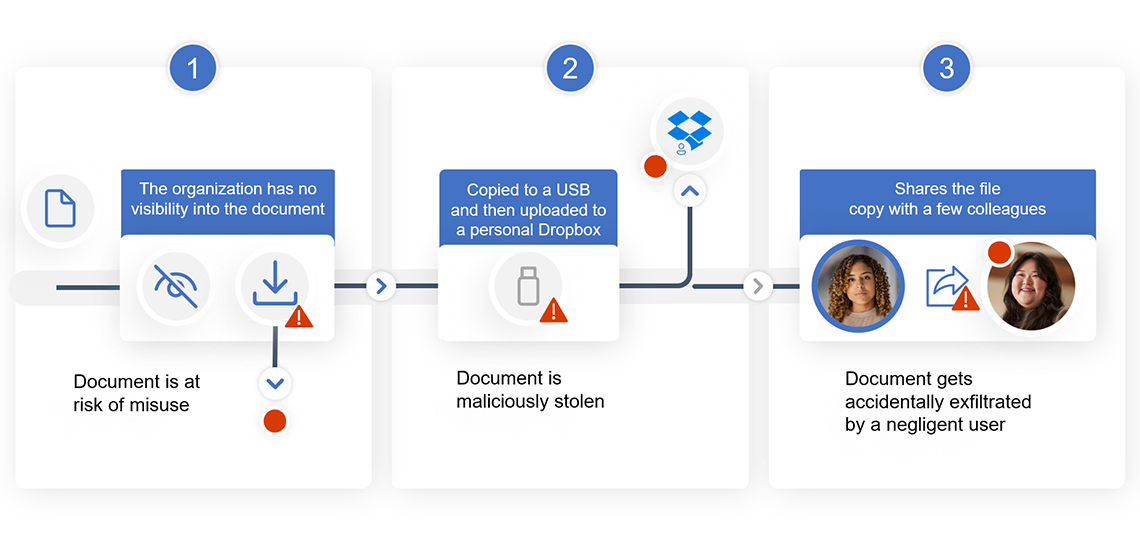
With more than 300 million people working remotely all over the world and collaborating across multiple environments and devices, data security incidents can happen anytime anywhere. There are three primary scenarios for data security incidents.
- If your organization doesn’t have visibility into its data – the data is at risk of misuse (exfiltration, exposure, etc.)
- If a user has malicious intent and is trying to exfiltrate the data
- If a user inadvertently takes a sensitive document and makes it visible
As organizations think about protecting their most important asset, their data, they ultimately need to create an in-depth approach to securing and defending it. There are three components to this strategy, but it is important to keep in mind that you don’t need to do these in any particular order. This strategy should be tailored to your own organization’s unique needs. Let’s break this down.
Protect Sensitive Data
It is important to understand and discover sensitive data within your organization. You need solutions that provide unparalleled visibility into your entire data estate, whether on-premises, hybrid, or multi-cloud. Microsoft Purview offers a single pane of glass which enables you to view and manage your data from one place, improving your team’s efficacy for data security. You can see the volume, type, and location of sensitive information in your data estate. Discovering the data is beneficial when you can put protection policies in place to keep that data safe. To protect you at this line of defense, Microsoft offers solutions to help you classify and label your data and apply productions such as RMS, encryption and more.
Manage Insider Risks
Data doesn’t move itself; people move data. With all data in organizations, you need to understand the user context and intent around the data to effectively protect it with the right policy. This next layer of defense takes into account user context to identify potential data risks and/or risky activities that may lead to data security incidents, enabling security teams to quickly take mitigating action. Since data loss is usually caused by internal actors, organizations need to take a holistic approach to managing insider risk, which brings together the right people, processes, training and tools.
Prevent Data Loss
The last layer of defense in this integrated in-depth approach is to prevent data loss or unauthorized use of data. Over 85% of organizations do not feel confident they can detect and prevent loss of sensitive data. Organizations need a way to balance protection and productivity, without compromising either. It’s critical to ensure the proper access controls are in place and policies are set to prevent actions like improperly saving, storing, or printing sensitive data.
Of course, underlying everything here, is a strong ecosystem of partners, third party apps/platforms and clouds, as an organization’s data isn’t typically just within the Microsoft environments. Microsoft’s aim is to make sure these layers are put in place to protect your data, no matter where it is.
It doesn’t matter where an organization begins this journey. Each layer makes your data security stronger. So, build out what is most critical to you right now as you look to develop your longer-term strategy. These components create an integrated and holistic data security strategy, helping you to keep your organization’s data safe, wherever it lives.
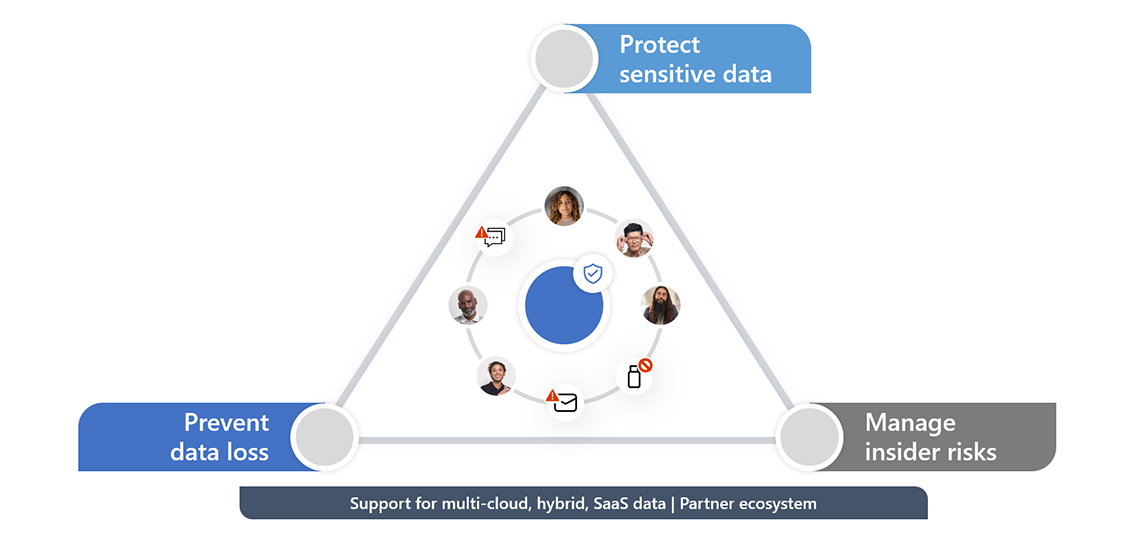
Microsoft Purview offers Information Protection, Insider Risk Management, and Data Loss Prevention on one unified platform that helps organization fortify data security effectively, so you can develop a defense-in-depth approach when it comes to protecting your sensitive data.
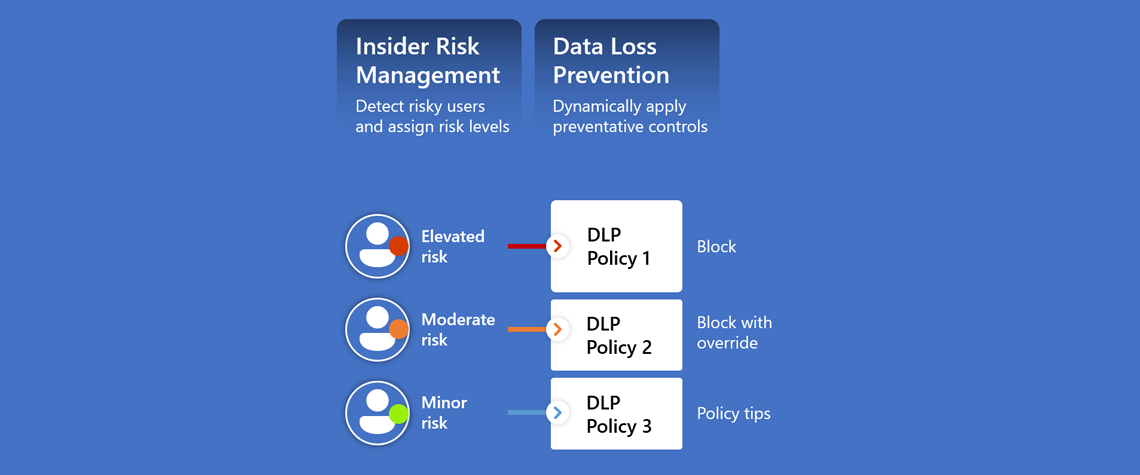
Organizations need all three defenses of protection to effectively secure data from potential data security incidents and they work better together with reinforced synergy across the platform. For example, if you use Information Protection and Data Loss Prevention together, you are able to discover and auto-classify the data and prevent it from unauthorized use. Using Information Protection and Insider Risk Management together, you can understand the user intent around sensitive data to identify the most critical data risks in your organization. Another example is if you use Insider Risk Management and Data Loss Prevention, then you can enable Adaptive Protection which assign appropriate DLP policies based on user’s risk levels. If you use all three products, then you can fortify your data security with a defense-in-depth approach.
A relatively new feature of Purview is the availability of Adaptive Protection, which helps you optimize data protection automatically.
In the past, admins might receive many alerts when files containing sensitive information were shared, transferred, copied, or printed. It could be overwhelming or resources-draining to triage and address all the alerts while there is limited support to prioritize them. With Adaptive Protection, admins can continuously detect the most critical risks with ML-driven analysis on both content and users, identifying sensitive data in motion performed by risky users, such as an employee who just submitted a resignation. Remember, data doesn’t move itself; people move data. By understanding the risk indicators of the user interacting with the data, admins can get more context-aware detection and reduce the overhead of reviewing an overwhelming number of alerts.
When you treat users with a static data protection policy, most of the time, the control would either be too loose that it didn’t help remediate data loss risks or too strict about blocking users from working productively. Adaptive Protection can change that by automatically adjusting the right level of remediation controls based on the risks detected, so high-risk users would be scoped in a stricter control while low-risk users can work as usual. Adaptive Protection it’s constantly adjusting, so the control could be dialed up or down when the user’s intent or behaviors change. The more precise remediation enables effective control enforcement while maintaining productivity.
Instead of treating risks separately in various solutions, Adaptive Protection brings signals and controls together across solutions. Below, you see how the risk indicators from Insider Risk Management and the data classification insights in DLP can help build a 1+1 > 3 protection. Organizations can take a defense-in-depth approach to prevent data loss, investigate insider risks, and leverage the integration between IRM and DLP to apply the right level of controls while maintaining productivity.
Why choose Microsoft Purview?
There are many data protection vendors in the industry, why is Microsoft Purview uniquely positioned to help organizations build a better data security strategy?
Here are three reasons.
First, it’s easy to get started and do not require you to go deploy agents. For example, with Information Protection you don’t need to train your classifiers – and can leverage auto-classification capabilities. With Insider Risk, you can run an Analytics report to identify trends and risks before even implementing a policy. And with Data Loss Prevention, you can leverage audit mode in a few simple clicks!
Second, Microsoft Purview products not only integrate across its platform to drive synergy, but also integrate with the most commonly-used productivity tools, such as Teams, Exchange, SharePoint, and OneDrive, so users get appropriate nudges as needed and can take actions to help protect data responsibly.
Lastly, Microsoft Purview offers built-in machine learnings capabilities to help discovery sensitive data, classify data, and detect the most critical risks around the data.
If you’re interested in learning more about Microsoft Purview or other security solutions, please leave us a note below.